Your Walls Are No Longer Walls
A piece of open-source software can map your body through them using only WiFi signals. No federal law prohibits it.
On March 8, 2026, Sam Bent, who posts on X as @DoingFedTime, was asked whether a Yagi antenna would stop the through-wall WiFi sensing software that had just gone viral on GitHub.1 His answer: “Not having wifi does.” When pressed, he added: “The attacker brings the router. You just have to be inside the signal path. I’ve never done this, so it’s an assumption.”
The first of those statements identifies a technical reality that the subsequent sections of this article document in detail: the target of CSI-based sensing does not need to own or operate any WiFi device, because the attacker supplies the transmitting hardware. The qualifying statement, that Bent had never personally deployed the technique, is worth noting precisely because the question is not whether any particular individual has done it. The question is whether the law has anything meaningful to say when someone can reconstruct a person’s body position, breathing rate, and heart rate from the other side of a wall, using hardware that costs $30, produces no detectable emission, and captures no image that any existing statute was written to address.
The answer, examined against the current state of federal law and constitutional doctrine, is almost nothing.
What WiFi DensePose Actually Does
In December 2022, researchers Jiaqi Geng, Dong Huang, and Fernando De la Torre at Carnegie Mellon University’s Human Sensing Laboratory completed a paper titled “DensePose From WiFi,” subsequently posted to arXiv as a preprint and submitted as a master’s thesis to the CMU Robotics Institute (arXiv:2301.00250).2 The paper described a deep neural network that maps the phase and amplitude of WiFi signals to UV coordinates across 24 regions of the human body, reconstructing full-body human pose in real time, through walls, without a camera.
The mechanism is a property of WiFi signals called Channel State Information, or CSI. CSI is not the data transmitted over a network. It is a measurement of how the signal traveled from transmitter to receiver, capturing amplitude and phase across dozens of individual frequency channels called subcarriers. A human body moving through a room disturbs those signal paths in ways that are consistent, measurable, and recoverable. A neural network trained on those disturbances can determine where a person is, how they are positioned, and whether their chest is rising and falling.
In early March 2026, a developer known as Reuven Cohen released an open-source implementation of the technique under the name RuView, also known as WiFi DensePose, on GitHub under an MIT license.3 The repository reached the top of GitHub’s trending lists within days.
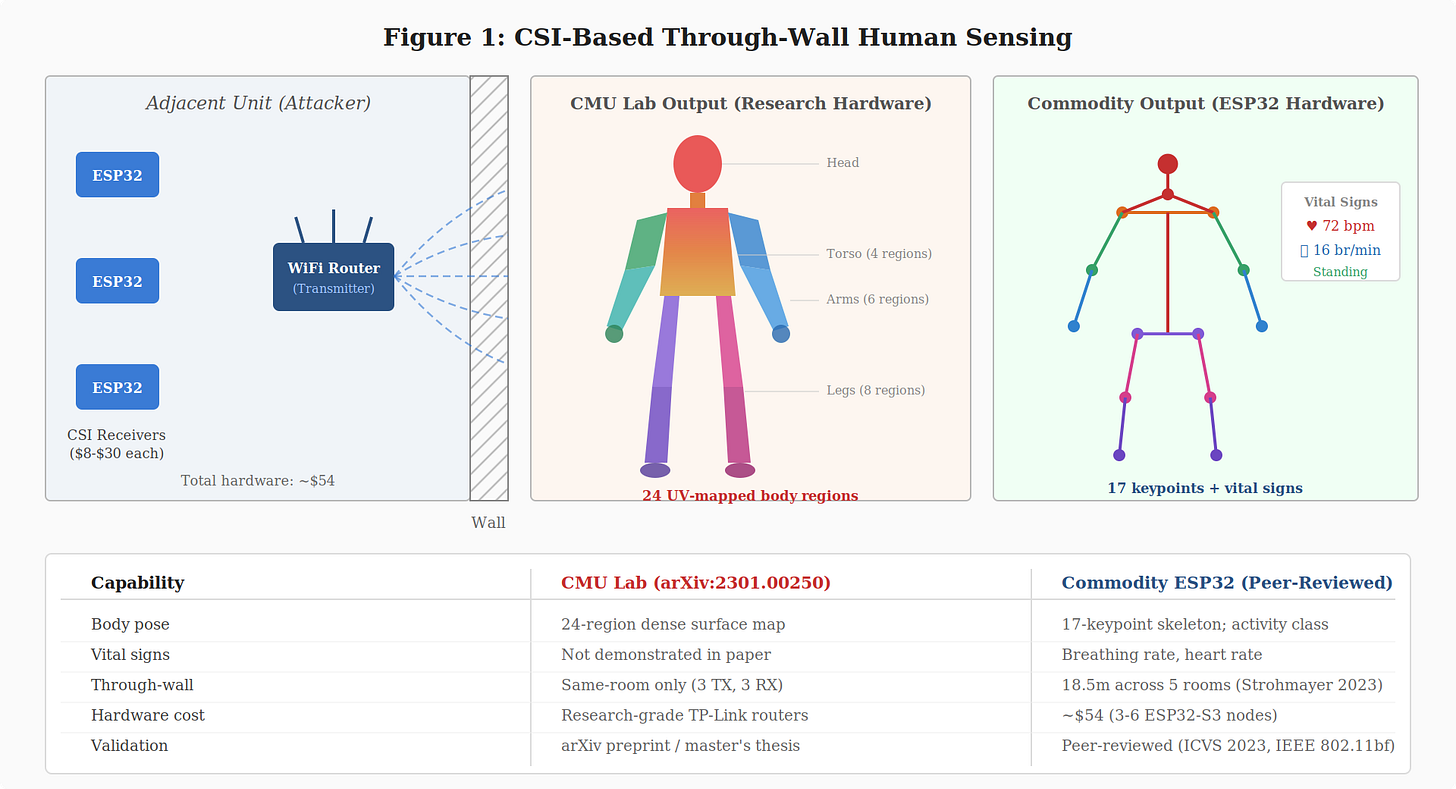
Figure 1. CSI-based through-wall human sensing at two capability levels. Left: the attacker deploys a WiFi transmitter and ESP32 receivers in an adjacent unit. Center: the CMU lab demonstrated a 24-region dense body surface map using research hardware (arXiv preprint, not peer-reviewed). Right: commodity ESP32 hardware, validated in peer-reviewed literature, produces a 17-keypoint skeleton with vital sign monitoring and has demonstrated through-wall activity recognition at 18.5 meters. The comparison table distinguishes what each capability level has actually demonstrated.
What It Actually Requires, and Why That Matters
Popular coverage has repeatedly misreported a critical technical distinction: a standard home router cannot perform this sensing. The GitHub repository states it directly. Full CSI-based pose estimation, vital sign monitoring, and through-wall detection require hardware that exposes per-subcarrier amplitude and phase data. Standard consumer WiFi equipment does not. The repository’s own documentation notes that consumer laptops “can only provide RSSI-based presence detection, which is significantly less capable.”3
What does work is an ESP32-S3 microcontroller, a commodity chip available from consumer electronics retailers for approximately $8 to $30. A functional sensing mesh requires three to six nodes plus a transmitting router; a documented starter configuration costs approximately $54 total. Alternatively, an Intel 5300 network interface card ($15 used, with modified firmware) or a Qualcomm Atheros AR9580 ($20 used, with kernel patches) can perform the same function.4
Peer-reviewed literature places the effective sensing range for commodity CSI hardware at approximately six to eight meters within a single room.5 Through-wall performance degrades with distance, but peer-reviewed research using ESP32-S3 hardware combined with a directional biquad antenna has demonstrated activity recognition across 18.5 meters spanning five rooms separated by 25-centimeter brick walls.6 A standard residential wall between adjacent units falls well within that range.
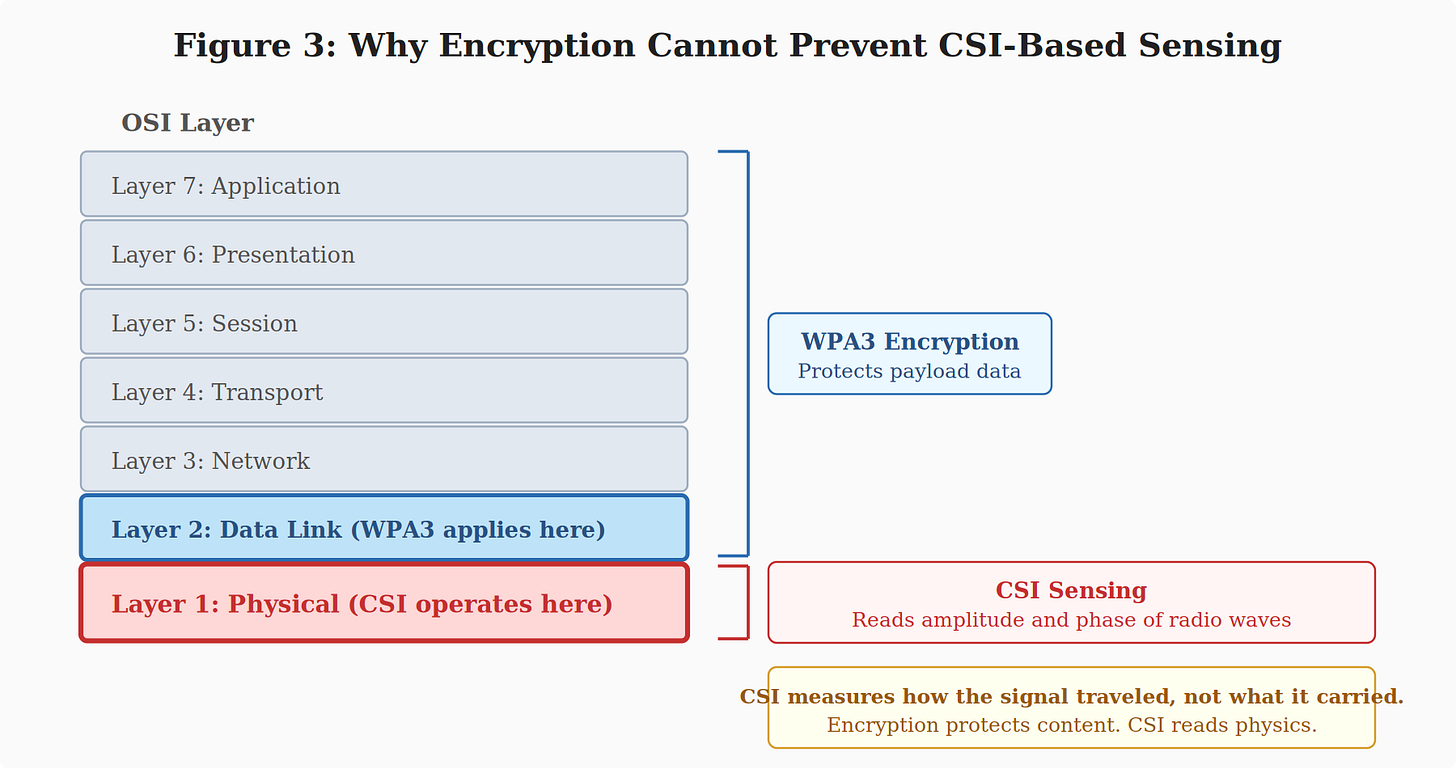
The Yagi question that prompted Bent’s response has a precise answer. A Yagi is a directional antenna that improves signal gain in one direction; it is relevant to transmitting or receiving radio signals, not to defending against sensing. CSI-based detection does not intercept data packets. It reads the physics of how radio waves scatter off a human body. WPA3 encryption is equally irrelevant: CSI operates at the physical layer of the radio signal, below the layer where any encryption is applied.7 What Bent identified correctly, even as an assumption, is that the attacker introduces their own transmitting hardware into the signal environment. The target does not need to own or operate any WiFi device. They need only to be present inside the signal path.
Figure 2. CSI operates at the physical layer (Layer 1) of the OSI model. Encryption protocols such as WPA3 protect payload data at Layer 2 and above. The amplitude and phase patterns of radio waves, which CSI reads, are unaffected by encryption.
One factual qualification is required before proceeding. The specific RuView/WiFi DensePose implementation has faced substantive criticism. Developers on Hacker News and GitHub identified code generating random CSI signals using np.random.rand() rather than actual hardware input, and alleged misrepresentation of cited research. Separate review flagged overnight inflation of the repository’s star count. The repository’s own audit log confirms that no real-world CSI dataset is bundled; the system runs on a synthetic reference signal.8 The underlying Carnegie Mellon research is a different matter. The CMU paper is an arXiv preprint and master’s thesis, not a peer-reviewed publication, but CSI-based human sensing as a field has been validated across hundreds of academic studies, deployed commercially at scale, and formally standardized by the IEEE under 802.11bf, published in September 2025.9 A two-year evaluation involving 280 edge devices across 16 real-world scenarios, processing more than four million motion samples, achieved 92.61% accuracy in diverse homes, and the resulting system now operates on over 100 million connected devices worldwide.9 Whether this specific GitHub implementation performs as advertised is a question about one developer’s repository. Whether the underlying capability exists is not. It does.
Two Separate Legal Problems
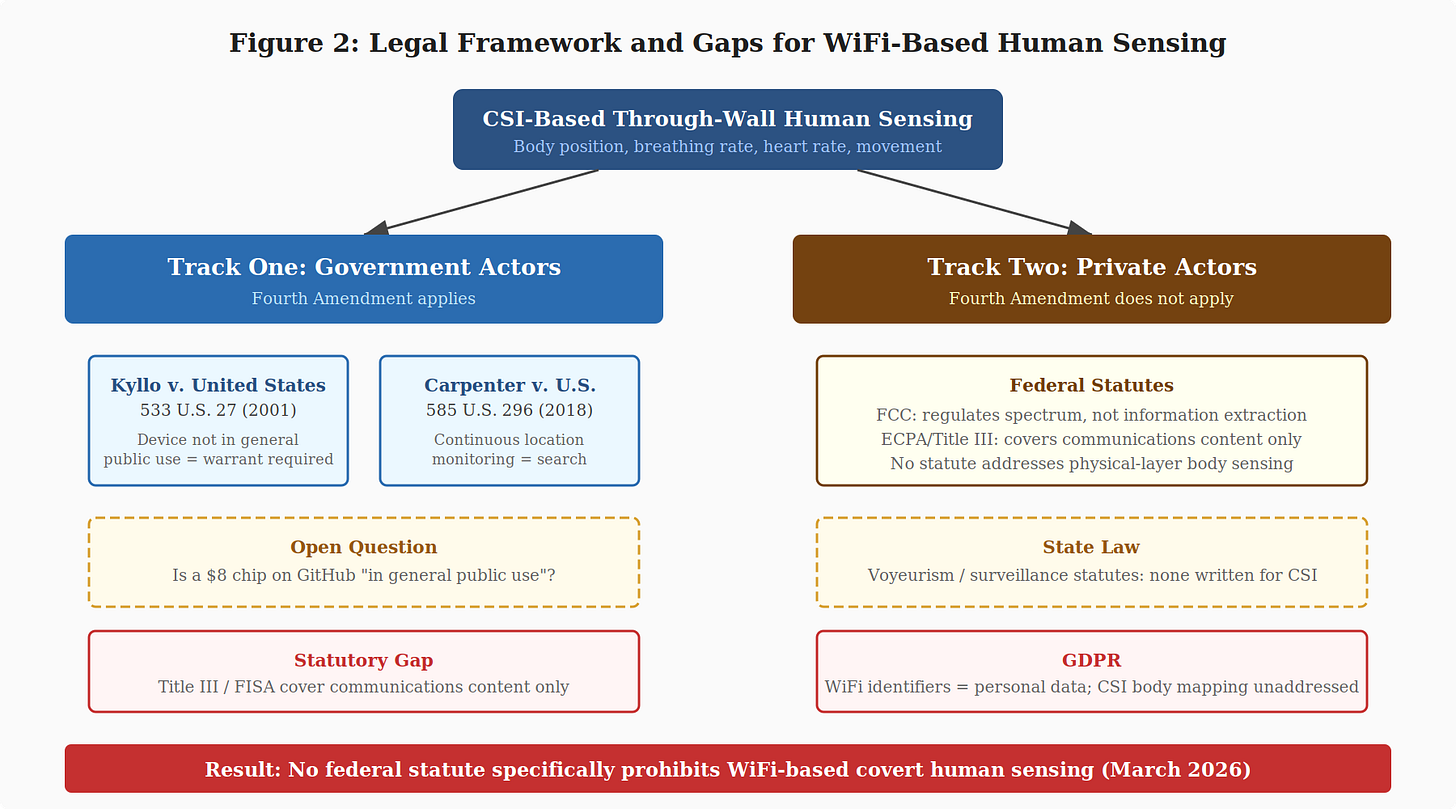
WiFi DensePose presents two distinct legal questions requiring separate analysis. The first is what happens when a government actor deploys it. The second is what happens when anyone else does. The answers are different, and both are incomplete.
Figure 3. The two-track legal analysis and the gaps within each track. For government actors, Kyllo and Carpenter provide constitutional grounds for requiring a warrant, but the “general public use” qualifier is unresolved and no statute specifically covers CSI sensing. For private actors, no federal statute prohibits it.
Track One: Government Actors
The Fourth Amendment stands, in the Supreme Court’s own formulation, most firmly at the threshold of the home. In Silverman v. United States, the Court declared that “[a]t the very core of the Fourth Amendment stands the right of a man to retreat into his own home and there be free from unreasonable governmental intrusion.”10 That principle has not weakened. Every major Fourth Amendment case addressing new surveillance technology in the decades since has returned to it.
The case that maps most directly onto WiFi DensePose is Kyllo v. United States, 533 U.S. 27 (2001). Federal agents used a thermal imaging device aimed at Danny Lee Kyllo’s home from a public street to identify heat patterns consistent with indoor marijuana cultivation. The Supreme Court, in a 5–4 opinion by Justice Antonin Scalia, held the surveillance was a Fourth Amendment search. The operative holding: where the government uses a device that is not in general public use to explore details of the home that would previously have been unknowable without physical intrusion, the surveillance is a “search” and is presumptively unreasonable without a warrant.11
The majority opinion was written deliberately to reach forward. The Court declined to limit the rule to thermal imaging and warned that restricting it would “leave the homeowner at the mercy of advancing technology, including imaging technology that could discern all human activity in the home.”11 Justice Scalia was describing a hypothetical risk. That hypothetical is now a $54 hardware kit running open-source software.
WiFi DensePose does not detect heat radiating through an exterior wall. It reconstructs body position, breathing rate, and heart rate of individuals inside the home, information that is by any defensible measure more intimate than the thermal distribution Kyllo addressed. Applied by a court willing to take the long view the majority invited, the Kyllo framework would require a warrant before government deployment of this technology against a private residence.
The open legal question is Kyllo’s “not in general public use” qualifier. The ESP32-S3 is a chip sold at consumer electronics retailers for as little as $8. Whether hardware at that price point, paired with a software stack available on GitHub, satisfies that threshold is a question no court has yet resolved. It bears noting that the Kyllo majority did not define “general public use” with precision, and the phrase has generated significant scholarly debate in the quarter-century since. A thermal imager that attaches to a smartphone is now available for approximately $200. Whether the availability of a technology in principle, as opposed to its widespread actual deployment for surveillance purposes, is the relevant metric is itself an unresolved doctrinal question.
A second line of authority bears on continuous monitoring. In Carpenter v. United States, 585 U.S. 296 (2018), the Supreme Court held that warrantless government acquisition of 127 days of historical cell-site location data constituted a Fourth Amendment search. Chief Justice Roberts’s majority opinion held that “an individual maintains a legitimate expectation of privacy in the record of his physical movements as captured through CSLI.”12 That holding was tied to cell-site location information specifically, but the reasoning extends naturally to CSI-based sensing, which captures a qualitatively different and more intimate category of data: not where a person traveled over a period of months, but how their body is positioned, whether they are breathing, and what their heart rate is, inside a private home, in real time. Carpenter’s logic, applied to that record, resolves in one direction.
The statutory gap remains even under this favorable constitutional reading. Title III of the Omnibus Crime Control and Safe Streets Act of 1968, codified at 18 U.S.C. § 2510 et seq., and the Foreign Intelligence Surveillance Act, 50 U.S.C. § 1801 et seq., were both designed around the interception of communications content. CSI-based sensing does not intercept communications. It reads radio wave physics. No court has ruled on whether existing statutory authority covers it.14
Track Two: Private Actors
The Fourth Amendment constrains only government action. It says nothing about what private actors may do.
There is currently no federal statute in the United States that specifically prohibits WiFi-based covert human sensing.13 The Federal Communications Commission’s statutory mandate centers on spectrum efficiency and interference prevention, not on restricting the information that can be extracted from an authorized transmission. The Electronic Communications Privacy Act of 1986 and Title III govern the interception of the contents of wire, oral, and electronic communications. CSI-based sensing does not intercept any communication. It reads the physical behavior of radio waves as they propagate through space and interact with a human body, operating below the layer that federal wiretapping law was written to address.14
State law provides no consistent alternative. Some states have voyeurism or surveillance device statutes that courts might stretch to cover this conduct. None were written with through-wall CSI body mapping in mind, and most have not addressed it at all.
Any private actor who deploys an ESP32-S3 mesh and uses it to monitor body position, sleep patterns, and vital signs through a wall is operating in a legal space that existing law has not closed. The European Union’s General Data Protection Regulation classifies WiFi tracking identifiers as personal data, but CSI-based body pose extraction, which produces a real-time skeletal map of a specific individual inside a specific dwelling, has not been specifically addressed by regulators on either side of the Atlantic.15
The Question the Law Has Not Answered
WiFi DensePose is not a camera. It captures no image. It produces no recording a person would recognize as surveillance footage. What it produces is a skeletal data structure, 17 body keypoints updated in real time, and a continuous stream of physiological readings. That output is invisible in the legal sense that matters most: no existing surveillance statute was written to reach it.
Traditional surveillance law was designed around evidence that maps onto statutory categories legislators anticipated. A camera produces an image. A listening device produces audio. A tracking device produces location data. CSI-based sensing produces none of them. The sensing apparatus produces no detectable emission of its own, though the hardware nodes that enable it must be physically deployed in the signal environment. The data it extracts is not something the subject ever chose to expose. It is recovered from the involuntary physics of a human body occupying a room, inside the space the constitutional order has always treated as the most protected.
In Kyllo, Justice Scalia wrote that the Court must “take the long view.”11 In 2001, the technology before the Court could determine whether someone was running high-intensity grow lights. The technology commercially available in 2026 can identify which room a person occupies, whether they are standing or supine, whether they are breathing at a normal rate, and what their heart rate is, through a wall, without their knowledge, for $54 in hardware.
The gap between those two facts is not a technical gap. It is a legislative one. And it is, at present, open.
Endnotes
1. Sam Bent (@DoingFedTime), posts on X, March 8, 2026. The first post (“Not having wifi does”) was published at 7:27 PM; the second (“The attacker brings the router…”) at 10:08 PM. Available at
2. Jiaqi Geng, Dong Huang, and Fernando De la Torre, Dense Human Pose Estimation From WiFi, CMU Robotics Institute Technical Report CMU-RI-TR-22-59 (August 2022); arXiv preprint arXiv:2301.00250 (submitted December 31, 2022). Available at https://arxiv.org/abs/2301.00250. This paper has not been published in a peer-reviewed journal or conference proceeding. It is a master’s thesis and arXiv preprint. It has been cited in subsequent peer-reviewed literature and forms the conceptual basis for the open-source implementation discussed in this article.
3. RuView GitHub repository (formerly WiFi DensePose), developer Reuven Cohen (ruvnet), MIT License. Available at https://github.com/ruvnet/wifi-densepose. Docker images and Rust crates were published on March 1, 2026; the repository reached GitHub’s trending lists by approximately March 5, 2026. See AIToolly, “RuView: WiFi DensePose for Real-time Pose, Vitals, Presence,” March 5, 2026. The repository states: “CSI-capable hardware required.” The repository’s documentation claims deployment via Docker “in approximately 30 seconds.”
4. On hardware costs: The RuView repository documents a starter kit of three to six ESP32-S3 nodes for approximately $54 total. Alternative CSI-capable hardware includes the Intel 5300 NIC ($15 used, with modified firmware) and the Qualcomm Atheros AR9580 ($20 used, with kernel patches). See Halperin et al., “Tool Release: Gathering 802.11n Traces with Channel State Information,” ACM SIGCOMM Computer Communication Review 41, no. 1 (2011): 53; Xie et al., “Commodity Wi-Fi-Based Wireless Sensing Advancements over the Past Five Years,” Sensors 24, no. 22 (2024): 7195, Table 11.
5. On sensing range: Xie et al., supra note 4, available at https://pmc.ncbi.nlm.nih.gov/articles/PMC11597943/ (“The existing sensing range is usually just 6–8 m within a single room”).
6. Julian Strohmayer and Martin Kampel, “WiFi CSI-Based Long-Range Through-Wall Human Activity Recognition with the ESP32,” in Computer Vision Systems: ICVS 2023, LNCS vol. 14253 (Springer, 2023), 41–50, https://doi.org/10.1007/978-3-031-44137-0_4. ESP32-S3 with 2.4 GHz biquad antenna; 18.5 meters across five rooms separated by 25 cm brick walls. Peer-reviewed conference proceedings.
7. CSI operates at the Physical Layer (Layer 1) of the OSI model. Encryption protocols such as WPA3 protect payload data at Layer 2 and above. See Xie et al., supra note 5, Section 2; Ma et al., “WiFi Sensing with Channel State Information: A Survey,” ACM Computing Surveys 52, no. 3 (2019): Article 46.
8. byteiota.com, “WiFi DensePose Hits GitHub #2: Real or AI-Generated Hype?” (March 2026), available at https://byteiota.com/wifi-densepose-hits-github-2-real-or-ai-generated-hype/. The repository’s own audit log (WITNESS-LOG-028) confirms: “Real-world CSI dataset bundled: No. Only synthetic reference signal (seed=42).”
9. IEEE Std 802.11bf™-2025, published September 26, 2025. See https://standards.ieee.org/ieee/802.11bf/11574/. On large-scale deployment: “Experience Paper: Scaling WiFi Sensing to Millions of Commodity Devices,” arXiv:2506.04322 (June 2025): two-year evaluation, 280 edge devices, 16 scenarios, 4+ million motion samples, 92.61% accuracy. System now deployed on 100+ million devices. See also NIST, “IEEE 802.11bf: Enabling the Widespread Adoption of Wi-Fi Sensing,” https://www.nist.gov/publications/ieee-80211bf-enabling-widespread-adoption-wi-fi-sensing.
10. Silverman v. United States, 365 U.S. 505, 511 (1961).
11. Kyllo v. United States, 533 U.S. 27 (2001). Opinion by Scalia, J. Operative holding at 533 U.S. at 40. “Long view” language at 533 U.S. at 35–36. Available at https://supreme.justia.com/cases/federal/us/533/27/.
12. Carpenter v. United States, 585 U.S. 296 (2018). Opinion by Roberts, C.J. “[A]n individual maintains a legitimate expectation of privacy in the record of his physical movements as captured through CSLI.” Slip op. at 11. The holding was tied to CSLI. Its extension to CSI-based sensing is the article’s analytical argument, not a direct application of the holding.
13. No federal statute enacted as of March 2026 explicitly addresses or prohibits covert CSI-based human sensing. The FCC’s authority under 47 U.S.C. § 301 et seq. centers on spectrum management, not information extraction. See 47 C.F.R. Part 15.
14. Title III, 18 U.S.C. § 2510 et seq. “Intercept” defined at § 2510(4) as acquisition of “contents” of communications. CSI sensing does not acquire contents; it reads physical propagation characteristics. Whether courts would extend “contents” to cover physical-layer body sensing is unresolved. See Justice Manual § 9-7.000, https://www.justice.gov/jm/jm-9-7000-electronic-surveillance.
15. GDPR (Regulation 2016/679) Art. 4(1), Recital 30 (WiFi identifiers as personal data). Whether CSI-derived biometric data falls under Article 9 special categories is unresolved.